Note: The product logic has been changed a lot, please ignore the token part of the design. We won’t create tokens for this project.
Since I was recently stolen and lost some USDC, after discussing it with Bruce, we designed a solution to prevent more people from being stolen.
To briefly introduce the process of being stolen, for some reason, I had to check the assets in my wallet on Zapper, but I haven’t visited the website for a long time. So I went to Google to search and found the first link (sponsored) was a phishing link (currently removed). I connected my wallet without carefully checking the signature information and approved it, which resulted in 4600 USDC being transferred out of my wallet. There were also other signatures later, and I already felt something was wrong, so I rejected the following signatures. If I continued to sign, other tokens would also be transferred out.
Due to the above experience, let’s summarize the points to pay attention to in the future:
- Don’t click on Google sponsored links.
- Leave some gas fee in the hot wallet, and important assets should be placed in a cold wallet.
- For any Web3 website, after confirming it is correct, it is recommended to bookmark it and confirm it with a second person.
For the third point, actually the first step of confirming correctness is very important and difficult for novices. Of course, even experienced users sometimes make mistakes. Currently, people solve this problem by starting from the blacklist angle, discovering problematic links and adding them to the blacklist, and then using some plugins for reminders. However, phishing websites are constantly emerging and appearing very quickly, so the blacklist needs to be updated in a timely manner. Moreover, before adding the link to the blacklist, it is highly likely that someone has already been scammed, so the effectiveness of the blacklist in anti-phishing is limited.
Through some simple data analysis, it is actually found that Web3 also follows the Pareto principle (80/20 rule), which means that 80% of users may use 20% of websites and projects (such as OpenSea, MetaMask, Zapper, etc.) most of the time. Therefore, 80% of phishing websites will imitate the 20% of popular websites and try various ways to phish.
So we can try to design a public good: a whitelist of trusted Web3 project domain names. Collect the official websites of the top 20% of Web3 products that 80% of Web3 users use the most to form a list of trusted website links. Then we can publicly provide it to others, for example, by integrating it into wallet plugins for anti-phishing reminders, or by searching and confirming on http://safeurls.xyz/ before accessing a website.
Of course, there may be a few questions here:
- How do we ensure that our website link whitelist is trustworthy?
- How can new website links be reliably updated to the whitelist?
- How do we ensure that the whitelist results are not tampered with?
- More questions from you.
We have designed a simple product form and its sustainable operating plan, which should be a decentralized human-driven “blockchain”:
We will need a website to display the whitelist of website links, which can be searched and queried.
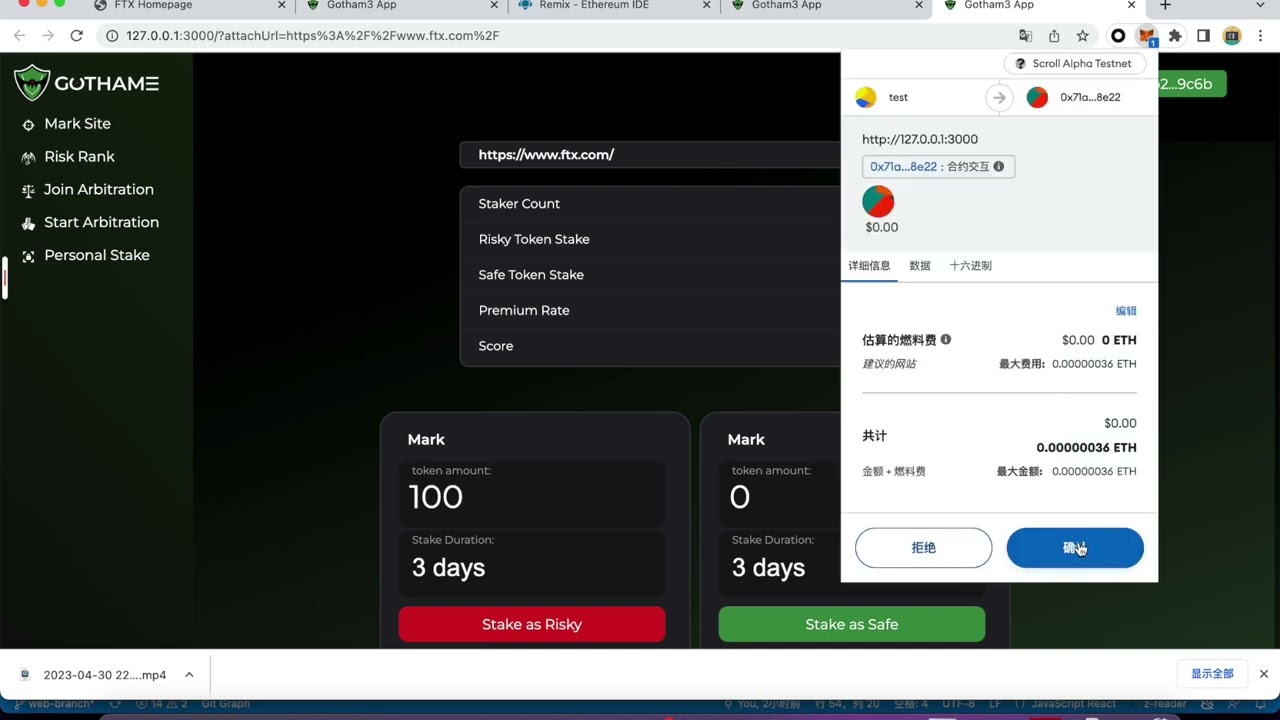
The entire operating plan references the PoW of the blockchain. First, the website link entering the whitelist requires review and submission of a task. We can package 5 URLs into one task and randomly broadcast it to 100 trusted nodes. The nodes must complete the review and voting within a specified time frame, and the results will be generated after the voting ends. The URL will either enter the whitelist or blacklist, and token rewards will be given to each participating node.
- We will issue tokens and recruit trusted nodes as initial reviewers. Currently, we are considering using Gitcoin passport scores as a metric for screening trusted nodes, and trusted nodes need to provide an email to receive subsequent task distribution.
- Any user who wants to submit a URL to the whitelist needs to buy tokens to do so. This can prevent some users from submitting spam or intentionally malicious URLs. Of course, any submitted URL will be reviewed and voted on by nodes. Therefore, if it is really a phishing link, it will go directly to the blacklist. The token spent on submitting URLs can also serve as a reward for nodes.
- If you are already a trusted node and want to submit a URL application, the “fee” for submitting the application can be discounted based on the “trustworthiness” of the node.
- We need to recruit as many trusted nodes as possible to increase the ability to process tasks concurrently and the accuracy of the validation results.
- When a task (5 URLs) is generated, it will randomly send emails to 100 trusted nodes (adjusted according to network capacity). Nodes need to complete validation and voting within 24 hours. We will not send more than 1 task to the same node per day. Validation takes time and tasks need to be distributed fairly.
- If there are too many tasks, more tokens can be spent to “cut in line” for processing. Nodes that receive urgent tasks will also receive more token rewards.
- The whitelist results should be stored in a decentralized permanent storage network, such as IPFS. If a whitelisted URL is attacked and needs to be removed, it can be reported and quickly executed the “whitelist to blacklist” operation. After recovery, it can be re-applied to join the whitelist.
- Finally, we can provide a whitelist interface to the outside world. Some wallet plugins or security plugins can be connected to provide necessary reminders during key operations.
There are still many details that need to be designed. If you are interested in the following technical points or theories, please join the discussion and implementation:
- Design of token economics
- How to make blockchain PoW design as open, transparent, and decentralized as possible
- Task assignment algorithm.
Chinese version below:
由于最近本人被盗,损失了一些 USDC,在跟 Bruce 讨论了之后,设计了一个方案来防止更多人被盗。
简单介绍一下被盗过程,因为一些原因我要去 Zapper 查看一下自己钱包里的资产,但是已经好久没有访问过这个网站,所以去了 Google 搜索,搜到的第一个链接(Sponsored)就是钓鱼链接(目前已被下架),连接钱包后没有仔细看签名信息就 approve 了,结果就是把我钱包里的 4600USDC 给转走了,后面还有其他的签名,我当时已经觉得不对劲了,所以就 reject 了后面的签名,如果继续签,其他 token 也会被转走。
因为以上的经历,先总结一下今后要注意的点:
- 不要点 Google sponsored 链接
- 热钱包就留一些 gas fee,重要资产放到冷钱包
- 任何 Web3 网站,确认无误后建议收藏一下,最好跟第二个人确认一下
对于第 3 点,其实第一步确认无误就是一件很重要且对于小白来说比较困难的事情,当然非小白有时候也会看走眼,目前大家解决此类问题都是从黑名单角度出发,发现有问题的链接就加到黑名单,然后会用一些插件来进行提醒,但是钓鱼网站是层出不穷的,并且出现的速度很快,所以黑名单的库要及时更新,并且把链接加到黑名单前大概率是已经有人被骗了,所以黑名单反钓鱼的效果有限。
经过一些简单的数据分析,其实 Web3 也是遵循帕累托法则(八二定律)的,也就是说 80% 的用户可能大部分时间用 20% 的网站和项目(例如 OpenSea、MetaMask、Zapper 等),所以 80% 的钓鱼网站会去模仿者 20% 的热门网站然后试图用各种方式进行钓鱼。
所以我们可以试图设计一个公共物品:可信 Web3 项目域名白名单的列表。收纳 Web3 80% 的人最常用到的 20% 的产品官网,形成一个可信网站链接白名单库。之后我们可以公开对外提供,比如接入钱包插件来做反钓鱼提醒,后者想访问某个网站,先来 http://safeurls.xyz/ 来进行搜索确认。
当然,这里可能会有几个问题:
- 如何保证我们的网站链接白名单是可信的?
- 新的网站链接如何可信的更新到白名单中?
- 如何保证白名单结果不被篡改?
- More questions from you
简单设计了一下产品形态以及它的可持续运作方案,这应该是一个去中心化的人力驱动的“区块链”:
我们会需要一个网站来展示白名单网站链接,可以进行搜索和数据查询。
整个运作方案参考了区块链的 PoW,首先网站链接进入白名单是需要审核的,进行任务提交,我们可以把 5 个 URL 打包成一个 task,随机广播给 100 个可信节点,然后节点要在规定时间内完成审核并完成投票,投票结束后产生结果,这个 URL 是进入白名单还是黑名单,最后奖励 token 到每一个参与投票的节点。
- 我们会先发币,招募可信节点作为初始审核员,目前想到可以用 Gitcoin passport 分数作为一个指标进行筛选可信节点,可信节点需要提供 email 来接收后续的审核 task 分发。
- 任何想要提交 URL 到白名单的用户,需要买 token 来进行提交,这样可以防止一部分乱提交的,或者故意作恶的用户,当然任何提交申请的 URL 会进行节点审核并投票,所以如果真的是钓鱼链接,会直接进入黑名单,相信黑客应该不会选择花了钱还自投罗网吧。提交 URL 花的 token 也可以作为节点的奖励。
- 如果你本身就是一个可信节点,想要提交 URL 申请,基于节点的“可信”,提交申请“费用”可以打折。
- 我们需要尽可能多的招募可信节点,提高并发处理 task 的能力以及验证结果的准确性。
- 当一个 task (5 个 URL)产生后,会随机发邮件给 100 个可信节点(按照网络容量调整),节点需要在 24 小时内完成验证并投票,我们一天不会发给同样的节点超过 1 个 task,验证需要时间,也需要公平分发 task。
- 如果 task 过多,可以花更多的 token 进行“插队”处理,那么分到紧急 task 的节点也会得到更多的 token 奖励。
- 白名单结果要存到去中心化的永久存储网络中,比如 IPFS。如果某个白名单 URL 被攻击需要移除,可以进行举报,并快速执行“白转黑”的操作,等恢复后可重新申请加入白名单。
- 最后,我们可以对外提供白名单接口,一些钱包插件或者安全插件可以接入,在重点操作时进行必要的提醒。
这里面还有很多细节需要设计,如果你对以下技术点或者理论感兴趣,欢迎加入讨论和实现:
- 代币经济的设计
- 区块链 PoW 设计如何尽可能公开透明去中心化
- 任务分配算法